As you're probably aware by now, since June 1st 2023 all well-known / public Certificate Authorities (CA) no longer provide Code Signing Certificates using pure software based private keys (see https://www.linkedin.com/posts/johannes-michler-099892ab_code-signing-key-storage-requirements-will-activity-7090432157688492032-jGvC).
Since I prefer using such a trusted / public CA to sign Java Applets (that are still crucial for Oracle E-Business Suite or Oracle Forms) I've recently had a look into how we can now sign those Java JAR files. Part 1 of this blog series introduced the topic and an available "Cloud Based" Code Signing Certificate provider: Signing EBS/Forms - Part 1
In this second part I well be covering how the code signing can be done on an E-Business Suite Application Server running on Oracle Linux 7 on Oracle Cloud Infrastructure (OCI).
Installing required libraries
The Certum SimplySignDesktop Application for Linux unfortunately is not usable entirely headless. I've talked to the support team of Certum, and unfortunately, they do not have any plans to provide a pure Command Line Interface (CLI) of the application. Nevertheless, I was able to run the application without installing a full "Desktop Manager" such as GNOME on Linux. For this, I first installed the following libraries:
yum install libxslt.x86_64 pulseaudio-libs-glib2.x86_64 libwebp.x86_64 wget https://www.rpmfind.net/linux/epel/8/Everything/x86_64/Packages/s/stalonetray-0.8.3-15.el8.x86_64.rpm yum install stalonetray-0.8.3-15.el8.x86_64.rpm
Stalonetray is a stand-alone freedesktop.org and KDE system tray for the X Window System. It has full XEMBED support, minimal dependencies, and works with virtually any EWMH-compliant window manager (see https://wiki.archlinux.org/title/stalonetray).
With this and an X-Forwarding Tool such as either PuTTY and X-Ming or (more user-friendly) Mobaxterm (https://mobaxterm.mobatek.net/), it is possible to run the SimplySignDesktop Application over SSH. It's best to test if that is working first using any available X application, e.g. xclock, which is often available even without a full desktop:
MobaXterm SSH Session with X11-Forwarding and xclock application
Installation and Configuration of SimplySignDesktop
Download the Linux version of SimplySignDesktop from here: https://files.certum.eu/software/SimplySignDesktop/Linux-RedHat/
Then install it as follows:
cd /home/oracle/certum sh SimplySignDesktop-2.9.8-9.1.6.0-x86_64-prod-centos.bin
It asks for the root password (whyever/unfortunately; as mentioned the application has a lot of room for improvements).
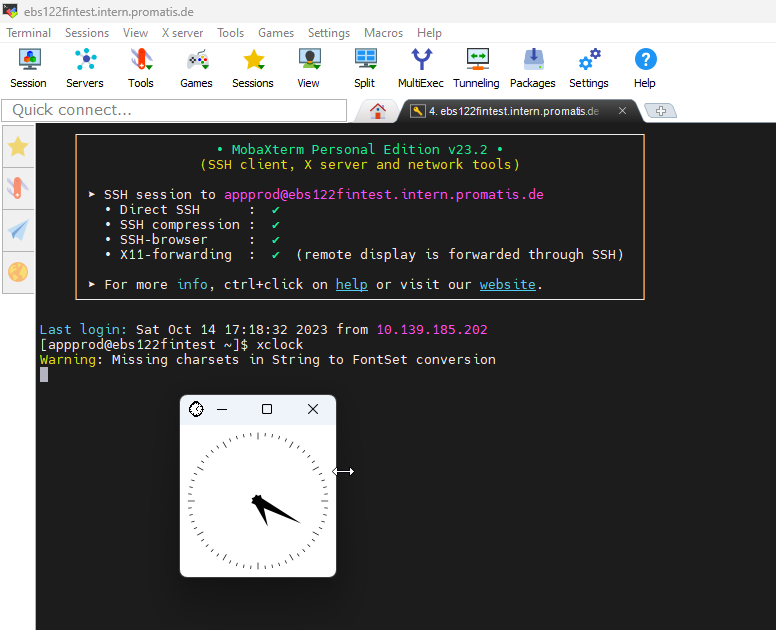
Then, still as the oracle user in an SSH Session with X-Forwarding start stalonetray, and then the Certum signing application:
stalonetray & /opt/SimplySignDesktop/SimplySignDesktop_start
This should show a small icon somewhere on your desktop through which you can sign in to the Certum Cloud Account using a one-time token generated on the Android App. If your keyboard does not allow to enter the username / token, it may be worth a try to use copy-paste instead.
You may furthermore need to use "Google translate" to translate from Polish to English. Did I mention that I don't really like the app? 😉
Certum SimplySign App headless on Linux
Keep that SSH Session and the SimplySignDesktop open and open a new SSH session. There, create the following file:
vi /home/oracle/provider_simplysign.cfg name=SimplySignDesktop/SimplySignPKCS library=/opt/SimplySignDesktop/SimplySignPKCS_64-MS-1.0.20.so slot=-1
Verification of Installation
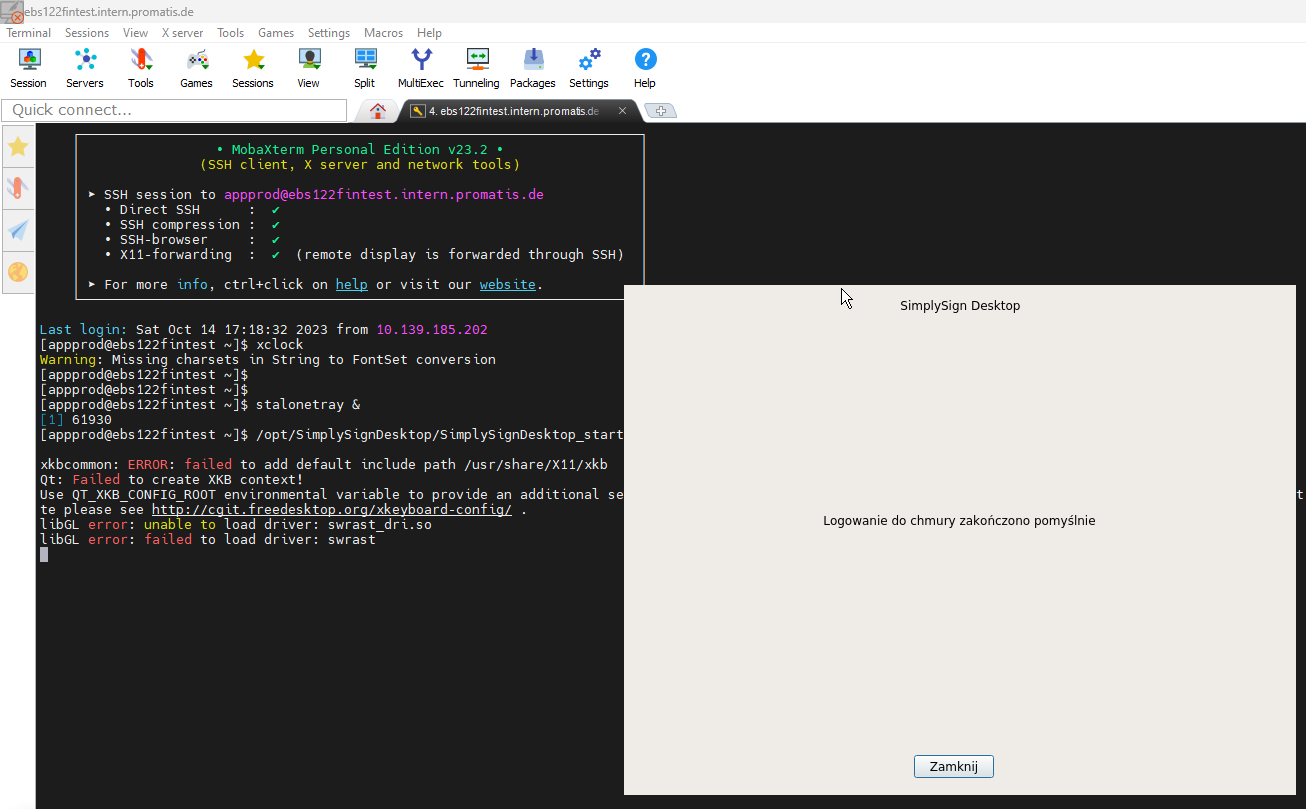
Then, you can check if everything is working with the following command:
/opt/proCertumSmartSign/jre/bin/keytool -list -keystore NONE -storetype PKCS11 -providerclass sun.security.pkcs11.SunPKCS11 -providerArg /home/oracle/provider_simplysign.cfg -v
You can use anything (e.g. 12345) as the password. That should show you your Code Signing Certificate purchased:
Output of jarsigner showing your code signing certificate
Note down the serial number (here: 7C66584B430CD378D0231CA224129EF4, that will be needed in the next step).
Then, create /home/oracle/certum/horuschain.pem containing the entire chain of (just put one after the other in the same file):
- Your own certificate (for me: C=DE, L=Ettlingen, OU=IT, O=Horus software Gmbh, CN=Horus software Gmbh/emailAddress=info@horus.biz)
- The intermediate certificate 1 (C=PL, O=Asseco Data Systems S.A., CN=Certum Code Signing 2021 CA)
- The intermediate 2 (C=PL, O=Unizeto Technologies S.A., OU=Certum Certification Authority, CN=Certum Trusted Network CA 2)
- The root certificate ( C=PL, O=Unizeto Technologies S.A., OU=Certum Certification Authority, CN=Certum Trusted Network CA)
First Signing
With those preparations in place, you can now sign a first .jar file:
/opt/proCertumSmartSign/jre/bin/jarsigner -keystore NONE -tsa "http://time.certum.pl" -certchain "/home/oracle/certum/horuschain.pem" -storetype PKCS11 -providerClass sun.security.pkcs11.SunPKCS11 -providerArg "/home/oracle/provider_simplysign.cfg" -storepass "12345" "ieucommon.jar" 7C66584B430CD378D0231CA224129EF4
That should provide a signed .jar file that you can again verify using:
jarsigner -verify -verbose -certs /u01/oracle/EBS122FT/ebs/fs1/EBSapps/comn/java/classes/oracle/apps/ieu/jar/ieucommon.jar
This should give you something similar to the following:
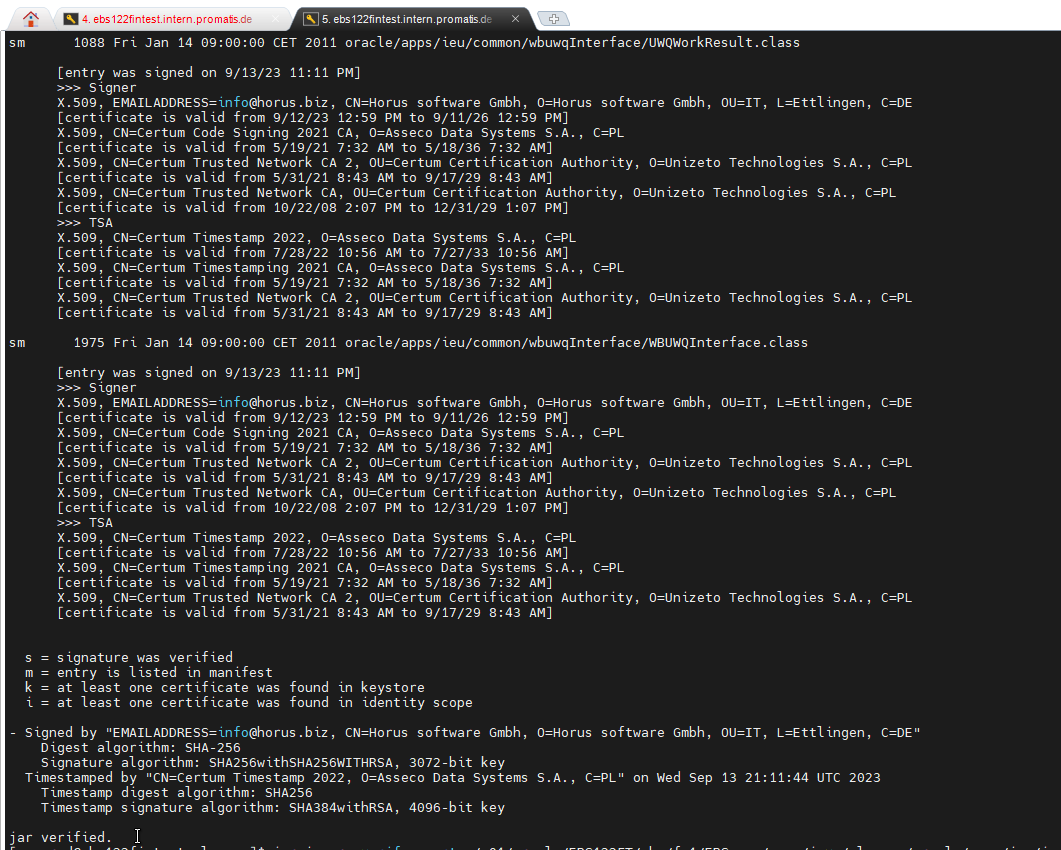
.jar file sucessfully verified
(Half-)Automating the signing
The last part is now to sign all the .jar files of E-Business Suite. As described in 2806640.1, the adadmin tool on signing creates a list of .jar files to be signed in $NE_BASE/EBSapps/log/adadmin/log/jarlist.txt.
I've implemented the following small sign.sh script which signs everything from that list:
adjarlist="$NE_BASE/EBSapps/log/adadmin/log/jarlist.txt"
# Select the jar files from jarlist.txt
jars_to_sign=`cat $adjarlist | grep '\.jar'`
for jar in ${jars_to_sign}
do
# Remove Signature from jar files created through ADADMIN in EBS
echo " ** Removing EBS signature from: ${jar} "
cp -i ${jar} /home/oracle/certum/backup_jars/
zip -d ${jar} 'META-INF/*.SF' 'META-INF/*.RSA'
/opt/proCertumSmartSign/jre/bin/jarsigner -keystore NONE -tsa "http://time.certum.pl" -certchain "/home/oracle/certum/horuschain.pem" -storetype PKCS11 -providerClass sun.security.pkcs11.SunPKCS11 -providerArg "/home/oracle/provider_simplysign.cfg" -storepass "12345" "${jar}" 7C66584B430CD378D0231CA224129EF4
done
After a restart of the application server that should allow you to sign into your E-Business Suite environment securely and without nasty errors again:
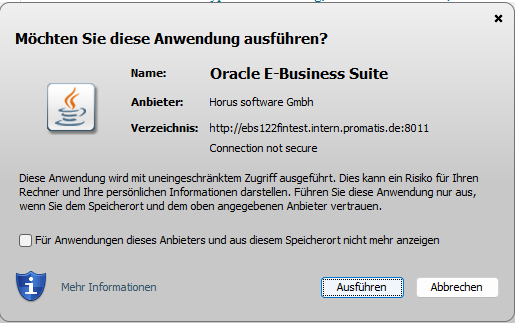
Dialog shown when opening a signed E-Business Suite environment
Summary
The above procedure allows you to sign all the .jar files of an E-Business Suite environment without copying the files to a different server. What I do not like so far thus is that I have to run that sign.sh shown above on/after every patch application. In an upcoming blog post, I will evaluate if there is a way to overwrite/overrule the built-in jarsigner command of adop/adadmin with the command shown above signing the code using Certum Cloud.


